Deck 2: Auditing IT Governance Controls
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال

فتح الحزمة
قم بالتسجيل لفتح البطاقات في هذه المجموعة!
Unlock Deck
Unlock Deck
1/99
العب
ملء الشاشة (f)
Deck 2: Auditing IT Governance Controls
1
Commodity IT assets easily acquired in the marketplace and should be outsourced under the core competency theory.
False
2
Some systems professionals have unrestricted access to the organization's programs and data.
True
3
Distributed data processing places the control IT recourses under end users.
True
4
An advantage of distributed data processing is that redundant tasks are greatly eliminated

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
5
Transaction cost economics (TCE)theory suggests that firms should outsource specific non-core IT assets

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
6
To improve control and efficiency,the CBIS tasks of new systems development and program maintenance should be performed by the same individual or group.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
7
An often-cited benefit of IT outsourcing is improved core business performance.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
8
A disaster recovery plan is a comprehensive statement of all actions to be taken after a disaster.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
9
Specific IT assets support an organization's strategic objectives.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
10
A ROC usually involves two or more user organizations that buy or lease a building and remodel it into a computer site,but without the computer and peripheral equipment.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
11
Commodity IT assets include such things are network management.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
12
Certain duties that are deemed incompatible in a manual system may be combined in a computer-based information system environment.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
13
In a CBIS environment,data consolidation protects corporate data from computer fraud and losses from disaster.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
14
To fulfill the segregation of duties control objective,computer processing functions (like authorization of credit and billing)are separated.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
15
A generally accepted advantage of IT outsourcing is improved security.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
16
The database administrator should be separated from systems development.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
17
To ensure sound internal control,program coding and program processing should be separated.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
18
RAID is the use of parallel disks that contain redundant elements of data and applications.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
19
A database administrator is responsible for the receipt,storage,retrieval,and custody of data files.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
20
Fault tolerance is the ability of the system to continue operation when part of the system fails due to hardware failure,application program error,or operator error.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
21
Systems development is separated from data processing activities because failure to do so
A) weakens database access security
B) allows programmers access to make unauthorized changes to applications during execution
C) results in inadequate documentation
D) results in master files being inadvertently erased
A) weakens database access security
B) allows programmers access to make unauthorized changes to applications during execution
C) results in inadequate documentation
D) results in master files being inadvertently erased

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
22
Supervision in a computerized environment is more complex than in a manual environment for all of the following reasons except
A) rapid turnover of systems professionals complicates management's task of assessing the competence and honesty of prospective employees
B) many systems professionals have direct and unrestricted access to the organization's programs and data
C) rapid changes in technology make staffing the systems environment challenging
D) systems professionals and their supervisors work at the same physical location
A) rapid turnover of systems professionals complicates management's task of assessing the competence and honesty of prospective employees
B) many systems professionals have direct and unrestricted access to the organization's programs and data
C) rapid changes in technology make staffing the systems environment challenging
D) systems professionals and their supervisors work at the same physical location

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
23
In a computer-based information system,which of the following duties needs to be separated?
A) program coding from program operations
B) program operations from program maintenance
C) program maintenance from program coding
D) all of the above duties should be separated
A) program coding from program operations
B) program operations from program maintenance
C) program maintenance from program coding
D) all of the above duties should be separated

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
24
Which organizational structure is most likely to result in good documentation procedures?
A) separate systems development from systems maintenance
B) separate systems analysis from application programming
C) separate systems development from data processing
D) separate database administrator from data processing
A) separate systems development from systems maintenance
B) separate systems analysis from application programming
C) separate systems development from data processing
D) separate database administrator from data processing

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
25
Which of the following is not an essential feature of a disaster recovery plan?
A) off-site storage of backups
B) computer services function
C) second site backup
D) critical applications identified
A) off-site storage of backups
B) computer services function
C) second site backup
D) critical applications identified

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
26
Which is the most critical segregation of duties in the centralized computer services function?
A) systems development from data processing
B) data operations from data librarian
C) data preparation from data control
D) data control from data librarian
A) systems development from data processing
B) data operations from data librarian
C) data preparation from data control
D) data control from data librarian

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
27
Some companies separate systems analysis from programming/program maintenance.All of the following are control weaknesses that may occur with this organizational structure except
A) systems documentation is inadequate because of pressures to begin coding a new program before documenting the current program
B) illegal lines of code are hidden among legitimate code and a fraud is covered up for a long period of time
C) a new systems analyst has difficulty in understanding the logic of the program
D) inadequate systems documentation is prepared because this provides a sense of job security to the programmer
A) systems documentation is inadequate because of pressures to begin coding a new program before documenting the current program
B) illegal lines of code are hidden among legitimate code and a fraud is covered up for a long period of time
C) a new systems analyst has difficulty in understanding the logic of the program
D) inadequate systems documentation is prepared because this provides a sense of job security to the programmer

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
28
A widespread natural disaster is a risk associated with a ROC.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
29
Adequate backups will protect against all of the following except
A) natural disasters such as fires
B) unauthorized access
C) data corruption caused by program errors
D) system crashes
A) natural disasters such as fires
B) unauthorized access
C) data corruption caused by program errors
D) system crashes

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
30
All of the following are issues of computer security except
A) releasing incorrect data to authorized individuals
B) permitting computer operators unlimited access to the computer room
C) permitting access to data by unauthorized individuals
D) providing correct data to unauthorized individuals
A) releasing incorrect data to authorized individuals
B) permitting computer operators unlimited access to the computer room
C) permitting access to data by unauthorized individuals
D) providing correct data to unauthorized individuals

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
31
A cold site backup approach is also known as
A) internally provided backup
B) recovery operations center
C) empty shell
D) mutual aid pact
A) internally provided backup
B) recovery operations center
C) empty shell
D) mutual aid pact

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
32
An advantage of a recovery operations center is that
A) this is an inexpensive solution
B) the initial recovery period is very quick
C) the company has sole control over the administration of the center
D) none of the above are advantages of the recovery operations center
A) this is an inexpensive solution
B) the initial recovery period is very quick
C) the company has sole control over the administration of the center
D) none of the above are advantages of the recovery operations center

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
33
For most companies,which of the following is the least critical application for disaster recovery purposes?
A) month-end adjustments
B) accounts receivable
C) accounts payable
D) order entry/billing
A) month-end adjustments
B) accounts receivable
C) accounts payable
D) order entry/billing

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
34
All of the following are control risks associated with the distributed data processing structure except
A) lack of separation of duties
B) system incompatibilities
C) system interdependency
D) lack of documentation standards
A) lack of separation of duties
B) system incompatibilities
C) system interdependency
D) lack of documentation standards

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
35
The major disadvantage of an empty shell solution as a second site backup is
A) the host site may be unwilling to disrupt its processing needs to process the critical applications of the disaster stricken company
B) intense competition for shell resources during a widespread disaster
C) maintenance of excess hardware capacity
D) the control of the shell site is an administrative drain on the company
A) the host site may be unwilling to disrupt its processing needs to process the critical applications of the disaster stricken company
B) intense competition for shell resources during a widespread disaster
C) maintenance of excess hardware capacity
D) the control of the shell site is an administrative drain on the company

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
36
Segregation of duties in the computer-based information system includes
A) separating the programmer from the computer operator
B) preventing management override
C) separating the inventory process from the billing process
D) performing independent verifications by the computer operator
A) separating the programmer from the computer operator
B) preventing management override
C) separating the inventory process from the billing process
D) performing independent verifications by the computer operator

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
37
A mutual aid is the lowest cost disaster recovery option,but has shown to be effective and low risk.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
38
Critical applications should be identified and prioritized by the user departments,accountants,and auditors.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
39
An advantage of distributed data processing is that individual end user groups set specific IT standards without concern for the broader corporate needs.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
40
The least important item to store off-site in case of an emergency is
A) backups of systems software
B) backups of application software
C) documentation and blank forms
D) results of the latest test of the disaster recovery program
A) backups of systems software
B) backups of application software
C) documentation and blank forms
D) results of the latest test of the disaster recovery program

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
41
A disadvantage of distributed data processing is
A)the increased time between job request and job completion.
B)the potential for hardware and software incompatibility among users.
C)the disruption caused when the mainframe goes down.
D)that users are not likely to be involved.
A)the increased time between job request and job completion.
B)the potential for hardware and software incompatibility among users.
C)the disruption caused when the mainframe goes down.
D)that users are not likely to be involved.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
42
Which of the following disaster recovery techniques may be least optimal in the case of a disaster?
A)empty shell
B)mutual aid pact
C)internally provided backup
D)they are all equally beneficial
A)empty shell
B)mutual aid pact
C)internally provided backup
D)they are all equally beneficial

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
43
The following are examples of specific assets except
A)application maintenance
B)data warehousing
C)highly skilled employees
D)server maintenance
A)application maintenance
B)data warehousing
C)highly skilled employees
D)server maintenance

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
44
Explain why certain duties that are deemed incompatible in a manual system may be combined in a CBIS computer based information system environment.Give an example.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
45
Which of the following is true?
A)Core competency theory argues that an organization should outsource specific core assets.
B)Core competency theory argues that an organization should focus exclusively on its core business competencies
C)Core competency theory argues that an organization should not outsource specific commodity assets.
D) Core competency theory argues that an organization should retain certain specific non-core assets in-house.
A)Core competency theory argues that an organization should outsource specific core assets.
B)Core competency theory argues that an organization should focus exclusively on its core business competencies
C)Core competency theory argues that an organization should not outsource specific commodity assets.
D) Core competency theory argues that an organization should retain certain specific non-core assets in-house.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
46
Which of the following is a feature of fault tolerance control?
A)interruptible power supplies
B)RAID
C)DDP
D)MDP
A)interruptible power supplies
B)RAID
C)DDP
D)MDP

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
47
Which of the following is not true?
A) Management may outsource their organizations' IT functions, but they cannot outsource their management responsibilities for internal control.
B) section 404 requires the explicit testing of outsourced controls.
C) The SAS 70 report, which is prepared by the outsourcer's auditor, attests to the adequacy of the vendor's internal controls.
D) Auditors issue two types of SAS 70 reports: SAS 70 Type I report and SAS 70 Type II report.
A) Management may outsource their organizations' IT functions, but they cannot outsource their management responsibilities for internal control.
B) section 404 requires the explicit testing of outsourced controls.
C) The SAS 70 report, which is prepared by the outsourcer's auditor, attests to the adequacy of the vendor's internal controls.
D) Auditors issue two types of SAS 70 reports: SAS 70 Type I report and SAS 70 Type II report.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
48
Segregation of duties in the computer-based information system includes
A) separating the programmer from the computer operator
B) preventing management override
C) separating the inventory process from the billing process
D) performing independent verifications by the computer operator
A) separating the programmer from the computer operator
B) preventing management override
C) separating the inventory process from the billing process
D) performing independent verifications by the computer operator

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
49
Which of the following is true?
A) Core competency theory argues that an organization should outsource specific core assets.
B) Core competency theory argues that an organization should focus exclusively on its core business competencies
C) Core competency theory argues that an organization should not outsource specific commodity assets.
D) Core competency theory argues that an organization should retain certain specific non-core assets in-house.
A) Core competency theory argues that an organization should outsource specific core assets.
B) Core competency theory argues that an organization should focus exclusively on its core business competencies
C) Core competency theory argues that an organization should not outsource specific commodity assets.
D) Core competency theory argues that an organization should retain certain specific non-core assets in-house.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
50
Which of the following is NOT a potential threat to computer hardware and peripherals?
A)low humidity
B)high humidity
C)carbon dioxide fire extinguishers
D)water sprinkler fire extinguishers
A)low humidity
B)high humidity
C)carbon dioxide fire extinguishers
D)water sprinkler fire extinguishers

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
51
Which of the following would strengthen organizational control over a large-scale data processing center?
A)Requiring the user departments to specify the general control standards necessary for processing transactions.
B)Requiring that requests and instructions for data processing services be submitted directly to the computer operator in the data center.
C)Having the database administrator report to the manager of computer operations.
D)Assigning maintenance responsibility to the original system designer who best knows its logic.
A)Requiring the user departments to specify the general control standards necessary for processing transactions.
B)Requiring that requests and instructions for data processing services be submitted directly to the computer operator in the data center.
C)Having the database administrator report to the manager of computer operations.
D)Assigning maintenance responsibility to the original system designer who best knows its logic.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
52
All of the following tests of controls will provide evidence about the physical security of the computer center except
A) review of fire marshal records
B) review of the test of the backup power supply
C) verification of the second site backup location
D) observation of procedures surrounding visitor access to the computer center
A) review of fire marshal records
B) review of the test of the backup power supply
C) verification of the second site backup location
D) observation of procedures surrounding visitor access to the computer center

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
53
All of the following tests of controls will provide evidence about the adequacy of the disaster recovery plan except
A) inspection of the second site backup
B) analysis of the fire detection system at the primary site
C) review of the critical applications list
D) composition of the disaster recovery team
A) inspection of the second site backup
B) analysis of the fire detection system at the primary site
C) review of the critical applications list
D) composition of the disaster recovery team

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
54
Which of the following is not true?
A) Large-scale IT outsourcing involves transferring specific assets to a vendor
B) Specific assets, while valuable to the client, are of little value to the vendor
C) Once an organization outsources its specific assets, it may not be able to return to its pre-outsource state.
D) Specific assets are of value to vendors because, once acquired, vendors can achieve economies of scale by employing them with other clients
A) Large-scale IT outsourcing involves transferring specific assets to a vendor
B) Specific assets, while valuable to the client, are of little value to the vendor
C) Once an organization outsources its specific assets, it may not be able to return to its pre-outsource state.
D) Specific assets are of value to vendors because, once acquired, vendors can achieve economies of scale by employing them with other clients

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
55
What are the three primary CBIS functions that must be separated?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
56
Which of the following disaster recovery techniques is has the least risk associated with it?
A)empty shell
B)ROC
C)internally provided backup
D)they are all equally risky
A)empty shell
B)ROC
C)internally provided backup
D)they are all equally risky

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
57
Which of the following is NOT a control implication of distributed data processing?
A)redundancy
B)user satisfaction
C)incompatibility
D)lack of standards
A)redundancy
B)user satisfaction
C)incompatibility
D)lack of standards

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
58
All of the following are recommended features of a fire protection system for a computer center except
A) clearly marked exits
B) an elaborate water sprinkler system
C) manual fire extinguishers in strategic locations
D) automatic and manual alarms in strategic locations
A) clearly marked exits
B) an elaborate water sprinkler system
C) manual fire extinguishers in strategic locations
D) automatic and manual alarms in strategic locations

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
59
Which of the following is not true?
A) When management outsources their organization's IT functions, they also outsource responsibility for internal control.
B) Once a client firm has outsourced specific IT assets, its performance becomes linked to the vendor's performance.
C) IT outsourcing may affect incongruence between a firm's IT strategic planning and its business planning functions.
D) The financial justification for IT outsourcing depends upon the vendor achieving economies of scale.
A) When management outsources their organization's IT functions, they also outsource responsibility for internal control.
B) Once a client firm has outsourced specific IT assets, its performance becomes linked to the vendor's performance.
C) IT outsourcing may affect incongruence between a firm's IT strategic planning and its business planning functions.
D) The financial justification for IT outsourcing depends upon the vendor achieving economies of scale.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
60
The following are examples of commodity assets except
A) network management
B) systems operations
C) systems development
D) server maintenance
A) network management
B) systems operations
C) systems development
D) server maintenance

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
61
What primary IT functions must be separated in a centralized firm?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
62
For disaster recovery purposes,what criteria are used to identify an application or data as critical?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
63
What is IT Governance?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
64
Describe two tests that an auditor would perform to ensure that the disaster recovery plan is adequate.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
65
What is an auditor looking for when testing computer center controls?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
66
Why should new systems development activities be segregated from the program change (maintenance)function.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
67
Briefly outline transaction cost economics as it relates to IT outsourcing.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
68
Why should the tasks of systems development and maintenance be segregated from operations?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
69
Describe the components of a disaster recovery plan.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
70
What is a recovery operations center? What is its purpose?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
71
Why is inadequate documentation a chronic problem?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
72
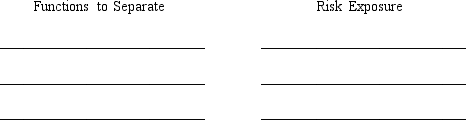
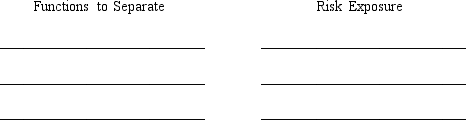
List three pairs of system functions that should be separated in the centralized computer services organization.Describe a risk exposure if the functions are not separated.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
73
. Why is poor-quality systems documentation a prevalent problem?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
74
What is RAID?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
75
What problems may occur as a result of combining applications programming and maintenance tasks into one position?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
76
Briefly explain the core-competency theory.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
77
What is a mirrored data center?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
78
The distributed data processing approach carries some control implications of which accountants should be aware.Discuss two.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
79
What exposures do data consolidation in a CBIS environment pose?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck
80
What are commodity IT assets?

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 99 في هذه المجموعة.
فتح الحزمة
k this deck








