Deck 10: Information Systems Controls for Systems Reliability Part 3: Processing Integrity and Availability
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال
سؤال

فتح الحزمة
قم بالتسجيل لفتح البطاقات في هذه المجموعة!
Unlock Deck
Unlock Deck
1/63
العب
ملء الشاشة (f)
Deck 10: Information Systems Controls for Systems Reliability Part 3: Processing Integrity and Availability
1
A customer failed to include her account number on her check,and the accounts receivable clerk credited her payment to a different customer with the same last name.Which control could have been used to most effectively to prevent this error?
A) Closed-loop verification
B) Duplicate values check
C) Validity check
D) Reconciliation of a batch control total
A) Closed-loop verification
B) Duplicate values check
C) Validity check
D) Reconciliation of a batch control total
A
2
A validity check is an example of a(n)
A) data entry control.
B) data transmission control.
C) output control.
D) input control.
A) data entry control.
B) data transmission control.
C) output control.
D) input control.
A
3
Sequentially prenumbered forms is an example of a(n)
A) data entry control.
B) data transmission control.
C) processing control.
D) input control.
A) data entry control.
B) data transmission control.
C) processing control.
D) input control.
D
4
Error logs and review are an example of
A) data entry controls.
B) data transmission controls.
C) output controls.
D) processing controls.
A) data entry controls.
B) data transmission controls.
C) output controls.
D) processing controls.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
5
Cancellation and storage of documents means that
A) data are copied from a document and stored, after which the document is shredded.
B) documents are defaced before being shredded.
C) documents are defaced and stored.
D) cancellation data are copied from documents before they are stored.
A) data are copied from a document and stored, after which the document is shredded.
B) documents are defaced before being shredded.
C) documents are defaced and stored.
D) cancellation data are copied from documents before they are stored.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
6
All of the following controls for online entry of a sales order would be useful except
A) check digit verification on the dollar amount of the order.
B) validity check on the inventory item numbers.
C) field check on the customer ID and dollar amount of the order.
D) concurrent update control.
A) check digit verification on the dollar amount of the order.
B) validity check on the inventory item numbers.
C) field check on the customer ID and dollar amount of the order.
D) concurrent update control.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
7
The data entry control that would best prevent entering an invoice received from a vendor who is not on an authorized supplier list is
A) a validity check.
B) an authorization check.
C) a check digit.
D) closed-loop verification.
A) a validity check.
B) an authorization check.
C) a check digit.
D) closed-loop verification.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
8
Which of the following data entry controls would not be useful if you are recording the checkout of library books by members?
A) Sequence check
B) Prompting
C) Validity check
D) Concurrent update control
A) Sequence check
B) Prompting
C) Validity check
D) Concurrent update control

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
9
Parity checks are an example of a(n)
A) data entry control.
B) data transmission control.
C) output control.
D) processing control.
A) data entry control.
B) data transmission control.
C) output control.
D) processing control.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
10
Batch totals are an example of a(n)
A) data entry control.
B) data transmission control.
C) output control.
D) processing control.
A) data entry control.
B) data transmission control.
C) output control.
D) processing control.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
11
If invoices are processed in groups of fifty,which fields from the document shown below would not be used to create a hash control total? 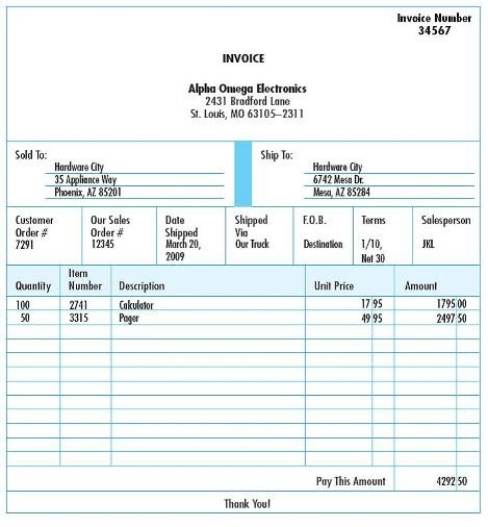
A) Amount
B) Item Number
C) Quantity Ordered
D) Sales Order number
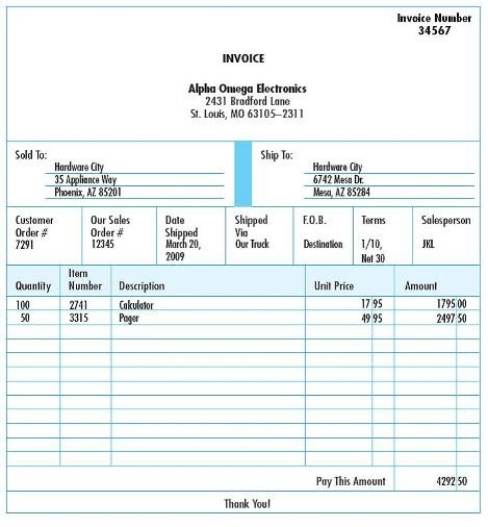
A) Amount
B) Item Number
C) Quantity Ordered
D) Sales Order number

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
12
When processing weekly payroll,an employee accidentally entered 400 for hours worked.The best data entry control for this error would be
A) a limit check.
B) a check digit.
C) batch total reconciliation.
D) a field check.
A) a limit check.
B) a check digit.
C) batch total reconciliation.
D) a field check.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
13
User reviews are an example of a(n)
A) data entry control.
B) data transmission control.
C) output control.
D) processing control.
A) data entry control.
B) data transmission control.
C) output control.
D) processing control.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
14
A specific inventory record indicates that there were 12 items on hand before a customer brings two of the items to the check stand to be purchased.The cashier accidentally entered quantity 20 instead of 2.Which data entry control would best have prevented this error?
A) sign check
B) limit check
C) validity check
D) field check
A) sign check
B) limit check
C) validity check
D) field check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
15
Turnaround documents are an example of a(n)
A) data entry control.
B) output control.
C) processing control.
D) input control.
A) data entry control.
B) output control.
C) processing control.
D) input control.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
16
A data entry input control in which the application software sums the first four digits of a customer number to calculate the value of the fifth digit and then compares the calculated number to the number typed in during data entry is an example of a
A) check digit verification.
B) validity check.
C) closed-loop verification.
D) duplicate data check.
A) check digit verification.
B) validity check.
C) closed-loop verification.
D) duplicate data check.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
17
Following is the result of batch control totals on employee Social Security Numbers in a payroll processing transaction: 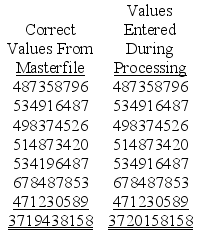 The difference in the control totals is 720,000.Which data entry control would best prevent similar data entry errors in the future?
The difference in the control totals is 720,000.Which data entry control would best prevent similar data entry errors in the future?
A) Modulus 11
B) Validity check
C) Check digit
D) Sequence check
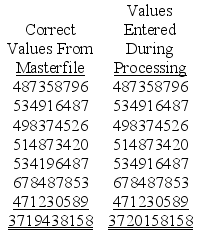 The difference in the control totals is 720,000.Which data entry control would best prevent similar data entry errors in the future?
The difference in the control totals is 720,000.Which data entry control would best prevent similar data entry errors in the future?A) Modulus 11
B) Validity check
C) Check digit
D) Sequence check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
18
The best example of a hash total for a payroll transaction file could be
A) total of employees' social security numbers.
B) sum of net pay.
C) total number of employees.
D) sum of hours worked.
A) total of employees' social security numbers.
B) sum of net pay.
C) total number of employees.
D) sum of hours worked.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
19
Data matching is an example of a(n)
A) data entry control.
B) data transmission control.
C) processing control.
D) input control.
A) data entry control.
B) data transmission control.
C) processing control.
D) input control.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
20
Forms design is an example of this type of control.
A) Data entry control
B) Processing control
C) Output control
D) Input control
A) Data entry control
B) Processing control
C) Output control
D) Input control

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
21
This ensures that the input data will fit into the assigned field.
A) Limit check
B) Range check
C) Size check
D) Validity check
A) Limit check
B) Range check
C) Size check
D) Validity check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
22
The Spontaneous Combustion Rocket Shoppe in downtown Fargo,North Dakota,generates three quarters of its revenue from orders taken over the Internet.The revenue clearing account is debited by the total of cash and credit receipts and credited by the total of storefront and Internet sales.This is an example of a
A) data integrity test.
B) zero-balance test.
C) trial balance audit.
D) cross-footing balance test.
A) data integrity test.
B) zero-balance test.
C) trial balance audit.
D) cross-footing balance test.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
23
This batch processing data entry control sums the number of items in a batch.
A) Financial total
B) Hash total
C) Record count
D) Sequence check
A) Financial total
B) Hash total
C) Record count
D) Sequence check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
24
This batch processing data entry control sums a non-financial numeric field.
A) Record count
B) Financial total
C) Hash total
D) Sequence check
A) Record count
B) Financial total
C) Hash total
D) Sequence check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
25
This control ensures that the correct and most current files are being updated.
A) Cross-footing balance test
B) Data matching
C) File labels
D) Write-protect mechanism
A) Cross-footing balance test
B) Data matching
C) File labels
D) Write-protect mechanism

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
26
This batch processing data entry control sums a field that contains dollar values.
A) Record count
B) Financial total
C) Hash total
D) Sequence check
A) Record count
B) Financial total
C) Hash total
D) Sequence check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
27
Chaz Finnerty called the IT Help Desk in a huff."I'm trying to open an Excel file and I get a message that says that the file is locked for editing.What's going on?" The answer is likely that
A) the file is corrupted due to a computer virus.
B) there is no problem. Chaz is editing the file, so it is locked.
C) concurrent update controls have locked the file.
D) Chaz probably opened the file as read-only.
A) the file is corrupted due to a computer virus.
B) there is no problem. Chaz is editing the file, so it is locked.
C) concurrent update controls have locked the file.
D) Chaz probably opened the file as read-only.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
28
When I enter a correct customer number,the data entry screen displays the customer name and address.This is an example of
A) prompting.
B) preformatting.
C) closed-loop verification.
D) error checking.
A) prompting.
B) preformatting.
C) closed-loop verification.
D) error checking.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
29
This determines if all required data items have been entered.
A) Completeness check
B) Field check
C) Limit check
D) Range check
A) Completeness check
B) Field check
C) Limit check
D) Range check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
30
File labels are an example of
A) data entry controls.
B) output controls.
C) processing controls.
D) source data controls.
A) data entry controls.
B) output controls.
C) processing controls.
D) source data controls.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
31
This tests a numerical amount to ensure that it does not exceed a predetermined value nor fall below another predetermined value.
A) Completeness check
B) Field check
C) Limit check
D) Range check
A) Completeness check
B) Field check
C) Limit check
D) Range check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
32
This data entry control compares the ID number in transaction data to a master file to verify that the ID number exists.
A) Reasonableness test
B) User review
C) Data matching
D) Validity check
A) Reasonableness test
B) User review
C) Data matching
D) Validity check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
33
Modest Expectations Investment Services (MEIS)allows customers to manage their investments over the Internet.If customers attempt to sell more shares of a stock than they have in their account,an error message is displayed.This is an example of a
A) reasonableness test.
B) field check.
C) validity check.
D) limit check.
A) reasonableness test.
B) field check.
C) validity check.
D) limit check.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
34
This determines if characters are of the proper type.
A) Field check
B) Alpha-numeric check
C) Range check
D) Reasonableness test
A) Field check
B) Alpha-numeric check
C) Range check
D) Reasonableness test

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
35
This control protects records from errors that occur when two or more users attempt to update the same record simultaneously.
A) Concurrent update controls
B) Cross-footing balance test
C) Data conversion controls
D) Recalculation of batch totals
A) Concurrent update controls
B) Cross-footing balance test
C) Data conversion controls
D) Recalculation of batch totals

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
36
Modest Expectations Investment Services (MEIS)allows customers to manage their investments over the Internet.If customers attempt to spend more money than they have in their account,an error message is displayed.This is an example of a
A) reasonableness test.
B) field check.
C) validity check.
D) limit check.
A) reasonableness test.
B) field check.
C) validity check.
D) limit check.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
37
This tests a numerical amount to ensure that it does not exceed a predetermined value.
A) Completeness check
B) Limit check
C) Range check
D) Sign check
A) Completeness check
B) Limit check
C) Range check
D) Sign check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
38
A computer operator accidentally used the wrong master file when updating a transaction file.As a result,the master file data is now unreadable.Which control could best have prevented this from happening?
A) Internal header label
B) Validity check
C) Check digit
D) Parity check
A) Internal header label
B) Validity check
C) Check digit
D) Parity check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
39
Check digit verification is an example of a(n)
A) data transmission control.
B) output control.
C) processing control.
D) input control.
A) data transmission control.
B) output control.
C) processing control.
D) input control.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
40
This determines the correctness of the logical relationship between two data items.
A) Range check
B) Reasonableness test
C) Sign check
D) Size check
A) Range check
B) Reasonableness test
C) Sign check
D) Size check

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
41
The accounting department at Synergy Hydroelectric records an average of 12,500 transactions per hour.By cost-benefit analysis,managers have concluded that the maximum acceptable loss of data in the event of a system failure is 25,000 transactions.The firm's recovery point objective is therefore
A) 25,000 transactions
B) 12,500 transactions
C) 1 hour
D) 2 hours
A) 25,000 transactions
B) 12,500 transactions
C) 1 hour
D) 2 hours

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
42
________ involves copying only the data items that have changed since the last partial backup.
A) Archive
B) Cloud computing
C) Differential backup
D) Incremental backup
A) Archive
B) Cloud computing
C) Differential backup
D) Incremental backup

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
43
What is the most effective way to ensure information system availability?
A) High bandwidth
B) Maintain a hot site
C) Maintain a cold site
D) Frequent backups
A) High bandwidth
B) Maintain a hot site
C) Maintain a cold site
D) Frequent backups

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
44
A facility that is pre-wired for necessary telecommunications and computer equipment,but doesn't have equipment installed,is known as a
A) cold site.
B) hot site.
C) remote site.
D) subsidiary location.
A) cold site.
B) hot site.
C) remote site.
D) subsidiary location.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
45
________ enables a system to continue functioning in the event that a particular component fails.
A) An incremental backup procedure
B) Fault tolerance
C) Preventive maintenance
D) A concurrent update control
A) An incremental backup procedure
B) Fault tolerance
C) Preventive maintenance
D) A concurrent update control

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
46
Probably the most important change management control is
A) monitoring user rights and privileges during the change process.
B) testing all changes thoroughly prior to implementation on a stand-alone computer.
C) updating all documentation to reflect changes made to the system.
D) management's careful monitoring and review.
A) monitoring user rights and privileges during the change process.
B) testing all changes thoroughly prior to implementation on a stand-alone computer.
C) updating all documentation to reflect changes made to the system.
D) management's careful monitoring and review.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
47
The accounting department at Synergy Hydroelectric records an average of 12,500 transactions per hour.By cost-benefit analysis,managers have concluded that the maximum acceptable loss of data in the event of a system failure is 25,000 transactions.If the firm's recovery time objective is 120 minutes,then the worst case recovery time objective is
A) 1 hour
B) 2 hours
C) 3 hours
D) 4 hours
A) 1 hour
B) 2 hours
C) 3 hours
D) 4 hours

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
48
________ copies all changes made since the last full backup.
A) Archive
B) Cloud computing
C) Differential backup
D) Incremental backup
A) Archive
B) Cloud computing
C) Differential backup
D) Incremental backup

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
49
The maximum acceptable down time after a computer system failure is determined by a company's
A) recovery time objective.
B) recovery point objective.
C) recovery objective.
D) maximum time recovery objective.
A) recovery time objective.
B) recovery point objective.
C) recovery objective.
D) maximum time recovery objective.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
50
Which of the following is not an objective of a disaster recovery plan?
A) Minimize the extent of the disruption, damage or loss.
B) Permanently establish an alternative means of processing information.
C) Resume normal operations as soon as possible.
D) Train employees for emergency operations.
A) Minimize the extent of the disruption, damage or loss.
B) Permanently establish an alternative means of processing information.
C) Resume normal operations as soon as possible.
D) Train employees for emergency operations.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
51
This control entails verifying that the proper number of bits are set to the value 1 in each character received.
A) Echo check
B) Field check
C) Parity check
D) Trailer record
A) Echo check
B) Field check
C) Parity check
D) Trailer record

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
52
The accounting department at Synergy Hydroelectric records an average of 10,000 transactions per hour.By cost-benefit analysis,managers have concluded that the maximum acceptable loss of data in the event of a system failure is 40,000 transactions.The firm's recovery point objective is therefore
A) 40,000 transactions
B) 10,000 transactions
C) 10 hours
D) 4 hours
A) 40,000 transactions
B) 10,000 transactions
C) 10 hours
D) 4 hours

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
53
A copy of a database,master file,or software that will be retained indefinitely as a historical record is known as a(n)
A) archive.
B) cloud computing.
C) differential backup.
D) incremental backup.
A) archive.
B) cloud computing.
C) differential backup.
D) incremental backup.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
54
The maximum amount of time between backups is determined by a company's
A) recovery time objective.
B) recovery point objective.
C) recovery objective.
D) maximum time recovery objective.
A) recovery time objective.
B) recovery point objective.
C) recovery objective.
D) maximum time recovery objective.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
55
A facility that contains all the computing equipment the organization needs to perform its essential business activities is known as a
A) cold site.
B) hot site.
C) remote site.
D) subsidiary location.
A) cold site.
B) hot site.
C) remote site.
D) subsidiary location.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
56
Which item below would not typically be part of an adequate disaster recovery plan?
A) a system upgrade due to operating system software changes
B) uninterruptible power systems installed for key system components
C) scheduled electronic vaulting of files
D) backup computer and telecommunication facilities
A) a system upgrade due to operating system software changes
B) uninterruptible power systems installed for key system components
C) scheduled electronic vaulting of files
D) backup computer and telecommunication facilities

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
57
While this type of backup process takes longer than the alternative,restoration is easier and faster.
A) Archive
B) Cloud computing
C) Differential backup
D) Incremental backup
A) Archive
B) Cloud computing
C) Differential backup
D) Incremental backup

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
58
The accounting department at Synergy Hydroelectric records an average of 10,000 transactions per hour.By cost-benefit analysis,managers have concluded that the maximum acceptable loss of data in the event of a system failure is 20,000 transactions.If the firm's recovery time objective is 60 minutes,then the worst case recovery time objective is
A) 1 hour
B) 2 hours
C) 3 hours
D) 4 hours
A) 1 hour
B) 2 hours
C) 3 hours
D) 4 hours

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
59
When a computer system's files are automatically duplicated on a second data storage system as they are changed,the process is referred to as
A) real-time mirroring.
B) batch updating.
C) consistency control.
D) double-secure storage.
A) real-time mirroring.
B) batch updating.
C) consistency control.
D) double-secure storage.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
60
Concerning system availability,which of the following statements is true?
A) Human error does not threaten system availability.
B) Proper controls can maximize the risk of threats causing significant system downtime.
C) Threats to system availability can be completely eliminated.
D) Threats to system availability include hardware and software failures as well as natural and man-made disasters.
A) Human error does not threaten system availability.
B) Proper controls can maximize the risk of threats causing significant system downtime.
C) Threats to system availability can be completely eliminated.
D) Threats to system availability include hardware and software failures as well as natural and man-made disasters.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
61
Define and contrast a recovery point objective and a recovery time objective.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
62
Discuss how cloud computing could both positively and negatively affect system availability.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck
63
Which of the following is true?
A) Cloud computing is a control technique for system availability.
B) Cloud computing eliminates the need for backup of applications and data.
C) Cloud computing refers to the practice of storing application files and backup data on satellites 'in the clouds'.
D) Cloud computing eliminates the need for companies to own their own software and servers.
A) Cloud computing is a control technique for system availability.
B) Cloud computing eliminates the need for backup of applications and data.
C) Cloud computing refers to the practice of storing application files and backup data on satellites 'in the clouds'.
D) Cloud computing eliminates the need for companies to own their own software and servers.

فتح الحزمة
افتح القفل للوصول البطاقات البالغ عددها 63 في هذه المجموعة.
فتح الحزمة
k this deck








